It is a given in today’s professional environments that people regularly discuss and share sensitive and confidential information on mobile devices. This in itself is a thread to business secrecy, personnel safety or financial transaction confidentiality. As interception technology is accessible and affordable under 10K USD, many unwanted third parties possess the tools to breach the confidentiality of your mobile voice and data communication - and even bigger is the number of businesses who bypass or neglect the protection of those frontiers.
Secfone shields your phone calls from various forms of attacks with its hardware-based protection and using our proprietary MVCN™ (Manageable Virtual Closed Network) security protocol. The encryption keys are stored on a smartcard module which provides a safety orders of magnitude better than software protection. MVCN™ is our patented proprietary security protocol responsible for server and peer authentication as well as establishing a secure communication channel between the correspondents. The main advantage of MVCN™ over other solutions is its matrix network topology structure which leaves no single point of attack for a possible external attack.
Benefits
- Encrypted VoIP voice calls and data traffic using hardware based protection
- True random encryption keys are generated and stored on an EAL 5+ crypto chip based cryptocard
- All calls handled through Secfone are invoiced as data traffic by the carrier networks: Wi-Fi, LTE (4G), HSDPA (3.5G), UMTS (3G), EDGE (2.5G), GPRS (2G), Satellite
- Peer-to-peer communication between corresponding parties
- Secure Email
- Secure SMS
- Sending attachment securely
- Secure conference calls
- Only certified apps can be installed onto Secfone Platinum
SECFONE
Platinum

The 5th generation Secfone Platinum is our flagship product, providing users with the highest possible level of mobile communication security.
Secfone Platinum comes as an out-of-the-box solution on a European designed and assembled Android smartphone. Secfone provides a pre-installed security layer and interface, as well as the Crypto Card with your unique cryptographic key to ensure that no sort of spyware, phishing software or ransomware is installed on your device before the first use. All essential parts have been checked by Navayo, the OS is a custom Android fork designed, compiled and signed by Navayo.
SECFONE for
Android & BlackBerry

Secfone is available for your Android and BlackBerry devices as well, with our flexible Crypto Card solution that transforms any device into a hardware-encrypted phone whenever you need secure communication. A cutting-edge choice for the discerning security-conscious users possessing sensitive or confidential information.
Secfone security
concept
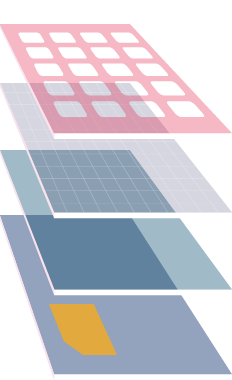
1 : Applications
- Authentication, Communication Encryption
- Resource manipulation control (microphone, speaker, etc)
- Secure voice, messaging, email, e.t.c.
2 : Security enhanced (hardened) OS
- Verified system components
- No Google services, no unauthorized deployments of apps
- No location reporting
- Rootkit protection
- Local content encryption 2
- OTA upgrades over encrypted channel
3 : Bootloader
- Ensures integrity of signed System and Recovery
4 : Verified Smartphone Hardware
- Secure boot (ensures Bootloader integrity)
5 : Secfone Cryptocard
- Hardware root of trust
- Provides PIN-restricted access to crypto functionality
- Tamper proof, EAL5+ certified hardware
- On-card key generation, True RNG 3 4 5